The Quad – the strategic security dialogue between Australia, India, Japan and the United States – is accustomed to dealing with threats to international security, including those emanating from the cyber domain. Indeed, in March 2021, the Quad Leaders made a commitment to “advance security and prosperity” and “address shared challenges, including in cyber space”.
The four governments appreciate the vital nature of cooperation on matters of cyber resilience – a point brought into sharp relief by the Director of the US Cybersecurity and Infrastructure Security Agency who remarked, “Everything is connected. Everything is interdependent. So, everything is vulnerable.”
In this context, the Quad is working to bolster software security under the Quad Cybersecurity Partnership (QCP). In May 2022, the four governments agreed to use their “collective purchasing power to improve the broader software development ecosystem”. In May 2023, they specifically committed to acquiring software that meets certain “high-level secure software development practices”.
In a working paper and policy brief for the German Institute for Global and Area Studies, I argue that these commitments form the missing link in the cyber diplomacy of the Quad governments. These governments have hitherto focused on the cobwebs, rather than the spider, in failing to target a major cause of our collective vulnerability as societies and economies: software insecurity. This is curious as much research from across stakeholder groups indicates that global software security is far from robust and cyber risk is increasingly being transmitted through software supply chains.
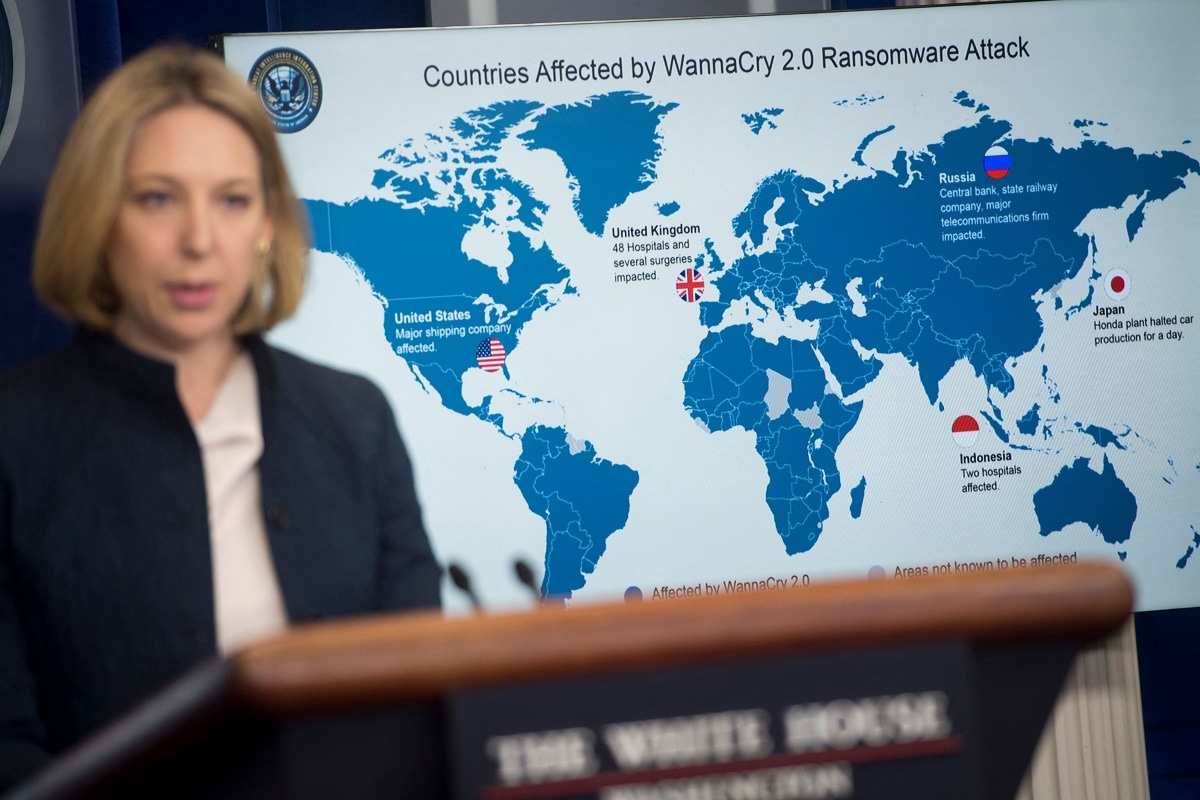
The systemic consequences of software insecurity were evident in the NotPetya and WannaCry attacks of 2017 that devastated the Ukrainian state and economy, and the British healthcare system, respectively. Attacks that were enabled by the exploitation of vulnerabilities in the Windows operating system.
And yet, software vendors such as Microsoft continue to market bug-laden code with seeming impunity, requiring end-users to clean up the mess. This is of critical importance when we consider how software is woven into the very fabric of our societies and economies.
It is well past time for governments to intervene and incentivise vendors to invest in the security of their software development life cycles (SDLCs). Broadly speaking, an SDLC is the process by which software is designed, created and maintained.
The Quad is betting on economic incentives – the opportunity for vendors to sell to the four governments. And by committing to amend their procurement regulations, the four governments are seeking to drive change in vendor behaviour faster than would be achieved through legislation, which may take a long time to draft, consult on and enact.
The significance of the Quad’s commitments is that the benefits will flow through to all societies and economies, not just those in the group. This is particularly enabled by two facts: American software vendors looking to sell to Quad governments dominate the global market, and the US government alone proposes spending of US$74 billion on IT for federal civilian agencies in the 2024 fiscal year. In aiming to qualify for US government procurement, software vendors will need to improve the security of their SDLCs, thereby improving the security of all their products. This benefits each of their users, not just their US government customers. The benefits are especially significant when the users are operators of critical infrastructure assets – systems vital to national security.
Implementation of the Quad’s software security commitments will enable and safeguard economic development around the world, given that secure digital technologies are critical to achieving the UN Sustainable Development Goals, in particular SDG 9, which centres on industry, innovation and infrastructure.
The Quad’s policy commitments also uphold the norms for responsible state conduct in cyberspace approved by the UN General Assembly in 2015, namely to “ensure the integrity of the [technology] supply chain”, including by requiring “vendors to incorporate safety and security in the design, development and throughout the lifecycle of ICT products”.
These policy commitments have a decent chance of being implemented because they drive the Quad’s internal credibility, and they build on its agenda to tackle cyber-enabled threats to security, including the central pillars of the QCP. They leverage the political will of each country to uplift software security. And the Quad Senior Cyber Group, which developed the software security principles underlying the commitments, enables the close working relationship required for the four governments to implement them.
We should also recognise that said software security principles are a template for any government to use for their procurement regulations, or indeed any vendor looking for guidance on how to harden their SDLCs. Indeed, the Quad has invited countries to “adopt these principles in pursuit of this shared vision for secure software”. In this fashion, the Quad’s policy commitments will position the grouping as a positive force for encouraging the cyber resilience of societies and economies while tackling the threats to national and international security that cyberspace enables.
The Quad’s efforts are carved out of the criticality of software security to our lives and livelihoods.
And so, this vital work carves the Quad in code.

